Charles Fisher brought to my attention that SSL encryption on KitKat is insecure (outdated) and susceptible to MITM (Man In The Middle) attacks when visiting secure websites using Privacy Browser. A MITM attack is performed by a third party that owns some of the network equipment between a browser and the website it is trying to visit. When a browser connects to a website, it negotiates the protocols and algorithms used for the connection, selecting the most secure options supported by both sides. By deleting or modifying packets during the initialization process, the MITM attacker can make it appear that the only commonly supported options are the really old ones (with known vulnerabilities). Specifically, SSLv3 and the RC4 algorithms are not secure. But if KitKat thinks these are the only available options, it will use them for communication with the website and the MITM can exploit the vulnerabilities in these older standards to read the encrypted data.
I spent some time looking at ways to mitigate these problems. It would be possible to override the default settings used by OpenSSL to disable the older, weaker algorithms, but doing so would either require embedding a custom WebView or bypassing the built-in WebView’s network commands and handling all the network requests and responses manually. As I have written on several occasions, it is likely that I will eventually include a custom WebView in Privacy Browser to provide greater privacy control, but the number of corner-case bugs this would introduce and the time commitment necessary to maintain a custom WebView and make sure it doesn’t introduce more security problems than it solves is significant. Currently Privacy Browser is a side project that I work on in my free time. Maintaining a custom WebView is not likely to be possible until Privacy Browser generates enough income that I can dedicate my full-time efforts to it.
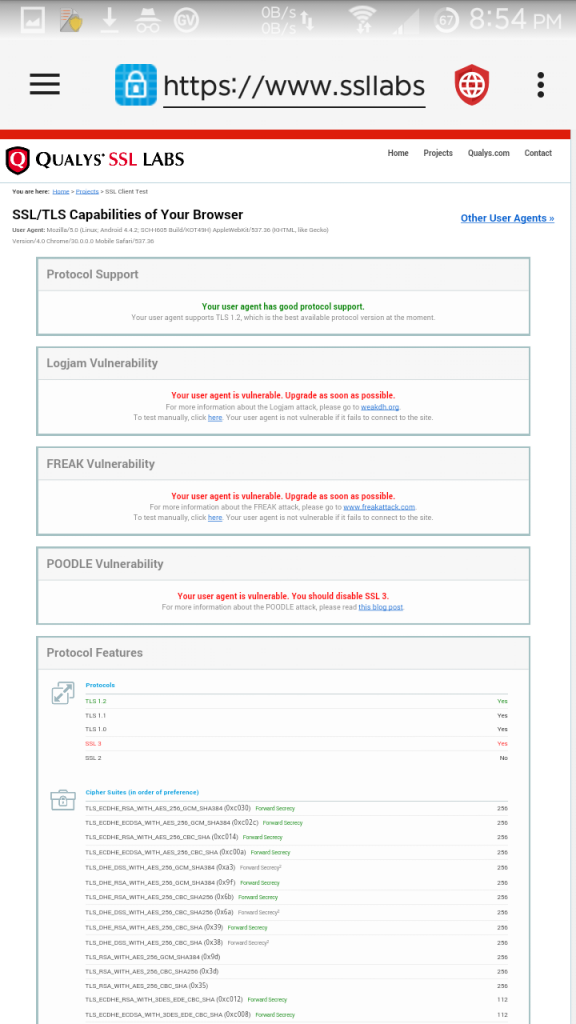
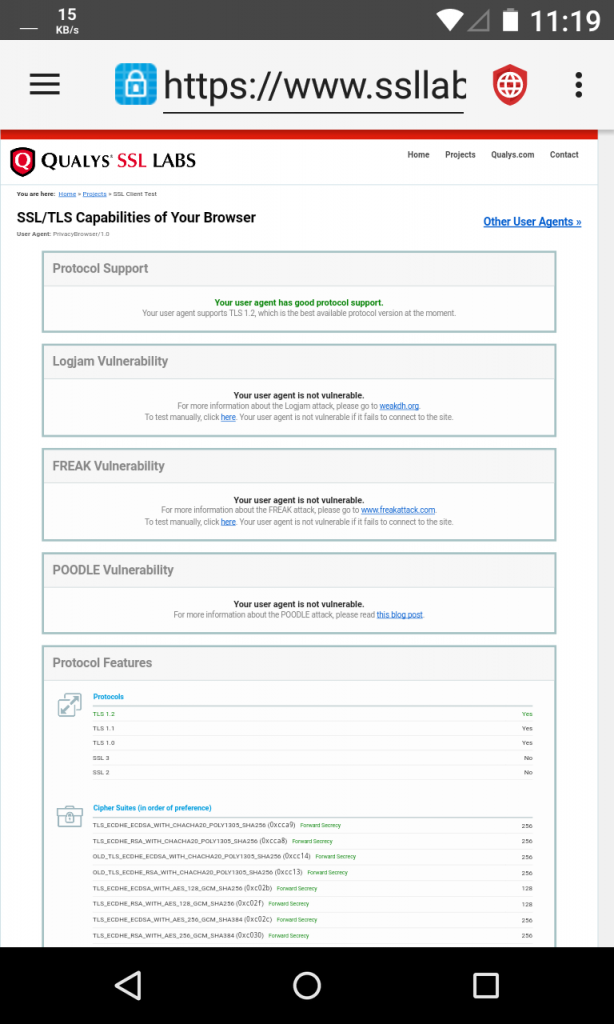
Beginning in Android Lollipop, the default Android SSL settings are sufficiently secure to prevent MITM attacks (SSLv3 and the RC4 based algorithms are disabled). You can test your browser at SSL Labs (JavaScript Required).
Currently 22.81% of Privacy Browser Free installs and 4.55% of Privacy Browser installs through Google Play are on devices running KitKat. F-Droid does not collect installation statistics, but my guess is that total KitKat usage does not exceed 25% (currently 25.2% of all devices that have connected to Google Play in the first seven days of November run KitKat). I considered bumping the minimum API from 19 to 21, which would disable KitKat support in future releases of Privacy Browser, but instead of doing so I am going to include a warning in the app description on the distribution channels. As of 18 November 2016, 20% of websites scanned by SSL Labs still support SSLv3 and 8.8% support weak ciphers like RC4. If you are worried about a nation state or ISP targeting you directly, you should not use Privacy Browser on KitKat (you should not use KitKat at all). However, if you only visit websites that have disabled the insecure protocols (SSL Labs allows you to test websites), then a MITM attack would not work even on KitKat because the weaker protocols must be supported by both sides to be used. Additionally, if you are primarily concerned about the tracking performed by web servers, Privacy Browser on KitKat will continue to fulfill those needs.
Thanks to Charles Fisher for testing a possible solution on KitKat (I don’t own a KitKat device, and emulator testing only goes so far) and for prividing the KitKat screenshot.