As some of you probably already know, the bulk of my current effort is being spent on building Privacy Browser PC. But a couple of weeks ago I came across an article explaining how 5G networks were designed with protections against interception by stingrays (IMSI catchers). For a long time I have been concerned with the poor the security of our cell phone protocols, but up until now I have never felt there has been anything I could do about it. Before reading the article I somehow hadn’t known that the 5G standard included some beefed up protection against stingrays, and I particularly didn’t know that 5G networks could run in either Standalone mode (SA) or in a mixed mode with 4G called Non-Standalone (NSA), where the control channel runs over the 4G protocol and only the data channel is 5G.
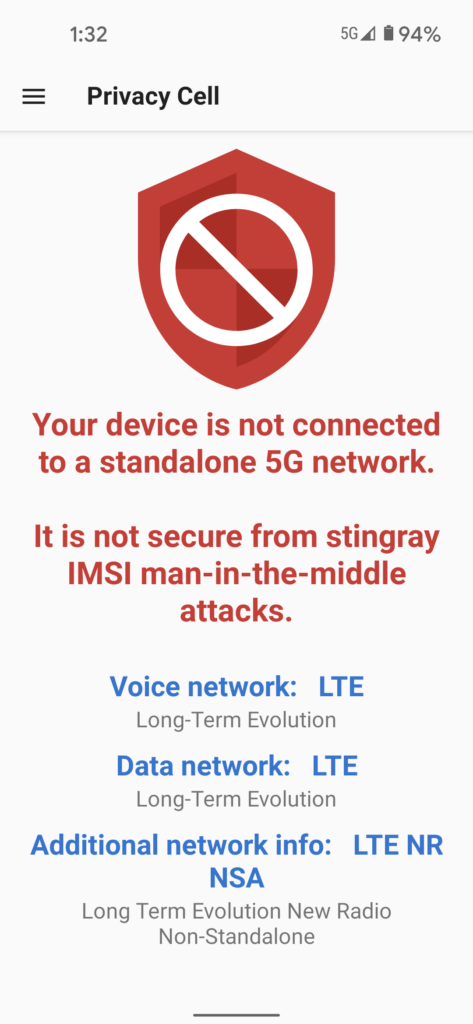
The concerning things about Non-Standalone mode is that it doesn’t provide the added protection against stingray interceptions. Even more concerning, the Android OS does not provide any indication of which type of network one is connected to. This means that, even after 5G SA becomes ubiquitous, a stingray can perform a downgrade attack and force a phone onto a 5G NSA network without the user having any indication that such has happened.
The article linked to above states that Android does provide apps access to the information necessary to tell if they are connected to a 5G SA or NSA network, and that there are several apps that expose that information. But it doesn’t actually link to or name any of them. Curious to see what type of 5G network I was connected to, I downloaded several promising apps and tried them out on my phone, but none of them gave me the information I was looking for. As part of my searching for an appropriate app, I came across the Android documentation describing how an app can access the necessary information and realized it only requires three commands. After a few minutes of frustration in not finding what I wanted in existing apps, I said to my wife, “I could just build an app that does this.” And thus was how Privacy Cell was born.
The core functionality only took one day to build. But all the other pieces—like a UI that doesn’t give you ulcers, and making it work correctly with the Android Activity Lifecycle, and writing the documentation—took several weeks to hammer out. However, I am pleased to announce that the first version of Privacy Cell is now available.
Privacy Cell requires Android 11 or higher because the commands necessary to probe the cell protocols were only added in Android 11 (API 30).
I have no intentions of directly monetizing Privacy Cell, although users are welcome to make donations if they so desire. Part of my reasoning is that Privacy Cell is a small program that didn’t take long to build and won’t require much maintenance after version 1.3 is released. The other part is that there is likely to be a halo effect, where users of Privacy Cell will also become aware of Privacy Browser, and will either purchase it or (hopefully) make a donation after downloading it from one of the sources where it is free.
Privacy Cell is currently working its way through the approval process on the various distribution channels, but those who are in a hurry can download it directly from stoutner.com.
