I recently received an email from a user asking a question about DNS and Tor which prompted me to think that a blog post on this topic would be helpful to users.
The email was concerned that DNS requests were not being proxied through Tor even when Privacy Browser was set to use Tor to proxy HTTP requests.
There is a movement afoot in recent years to have browsers ignore the OS DNS settings and implement DNS on their own. This is part of some companies’ belief that the browser should become the operating system, which is the exactly opposite of Privacy Browser’s core privacy and security design.
In Privacy Browser, when selecting a proxy through the options menu, that proxy handles HTTP and HTTPS traffic. It does not replace the OS DNS settings. Not only does this follow the good design guidelines of having the OS handle DNS instead of the browser, but it also is a limitation in Android’s WebView, meaning that there is no easy way to override this behavior even if I wanted to.
When proxying through Tor, this hides the user’s IP address from the websites they are visiting. Although the actual privacy benefit of this is less than most people assume, I provide it as an option that is beneficial in a few small cases. However, this proxying does not hide the user’s IP address from the DNS servers they are using to resolve URLs.
So, if a user is proxying through Tor using Privacy Browser, and they want to visit stoutner.com, they first do a DNS lookup on stoutner.com, which sends a request to the system-wide DNS server configured on their device. Once they receive the IP address back from the DNS server, then they send HTTPS requests over the Tor network.
If the user is visiting a .onion site, then the device first makes a DNS request to the OS configured DNS servers, which fails with a NXDOMAIN code. Privacy Browser then asks the proxy if it knows what to do with such an address, which Tor does.
The implications of this is that whatever DNS server you are using knows which websites you are visiting, even if they are .onion websites. This is why it is foolish to centralize your DNS servers into massive internet companies, like Google or Cloudflare, who advertise free DNS services to everyone on the internet out of the goodness of their hearts.
Understandably, users can be concerned about what DNS services they are using and how much information those services are collecting about them. Privacy Browser isn’t the place to resolve those concerns, but the purpose of this post is to explain a few options users have to modify those settings at the OS level.
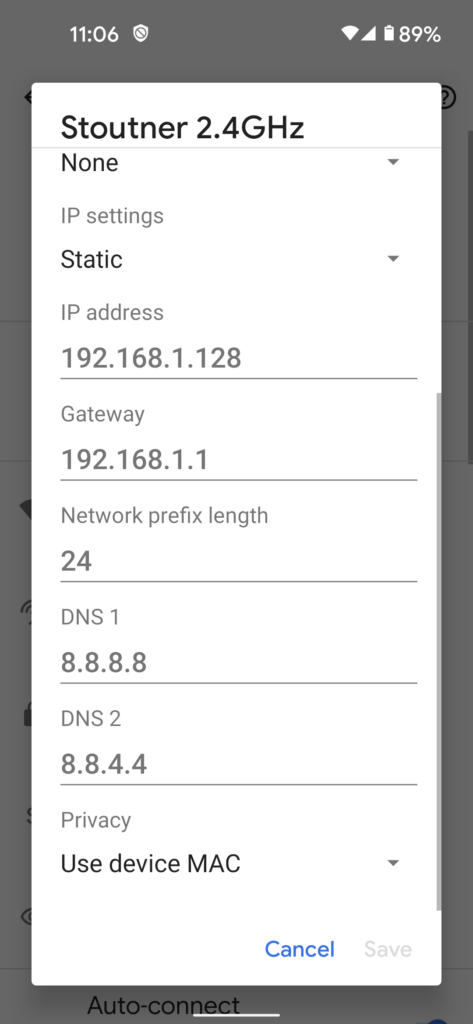
The first of these options is to use the OS static IP settings to specify the desired DNS servers. This is nice because it uses built-in OS tools. But it is cumbersome because it must be specified for each Wi-Fi network and because it cannot be used to control DNS settings when connected over a cell phone network.
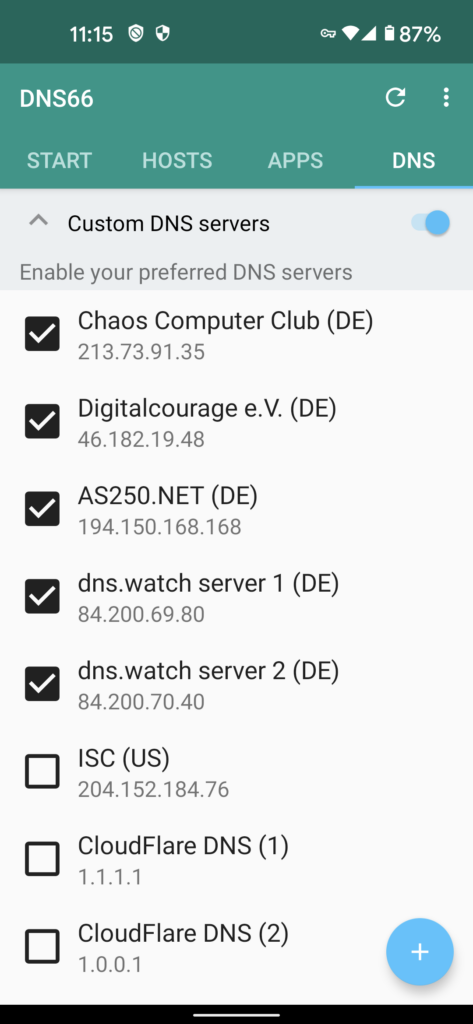
To provide more DNS controls, including the ability to set one DNS setting system-wide for all connections including cell networks, you can use an app like DNS66. It does this by using Android’s VPN APIs to force all DNS traffic through the app. When enabled, the VPN key icon will appear in the status bar on the right-hand side.
Orbot also contains the option to redirect DNS requests using Android’s VPN APIs. This is valuable for people who want to use Tor for all their traffic, including DNS.
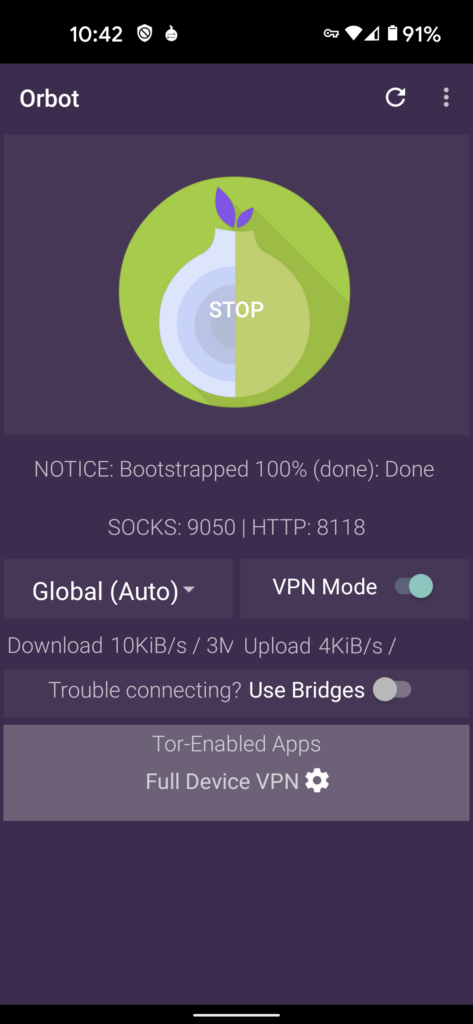
Note that when using Orbot in VPN mode, all traffic from Privacy Browser as well as everything else on the device will transit Tor, even without enabling the Tor proxy option inside of Privacy Browser. However, if you would like to visit a .onion website you will need to enable the Tor proxy inside of Privacy Browser or the URL lookup will fail.
